Access Control Systems Made Simple
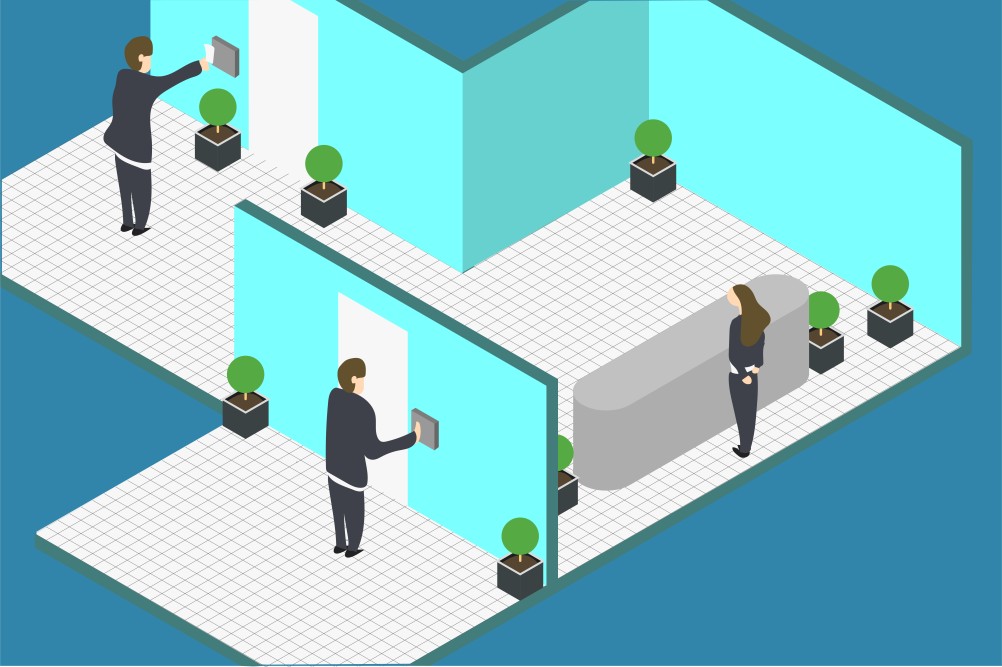
Access Control Systems Explained
Over the years, have controlled the passage of individuals in and out of numerous buildings. From the standard lock and key access control system, it eventually evolved into a more sophisticated computer-based system that makes use of electronic cards.
At present, access control systems are commonly used by organizations to provide quick and convenient access to authorized personnel while restricting access to intruders. In this blog, you’ll be able to learn more about this technology and make the most out of its capabilities. With this knowledge, you’ll be able to create smart decisions when you let reputed install it on your business site.
Components of an Access Control System

Now that you’re acquainted with the concept of access control systems, it’s time for you to learn and understand some of its components. Evidently, these systems vary a lot in type and complexity. Even though this is true, most of these systems consist of these basic components:
-
Access Cards
The access card is an electronic key that authorized people use to gain access to the areas secured by access control systems. Each of these cards is uniquely encoded to foster an accurate identification system. You can think of the access card as a modernized version of the olden day’s brass key. But instead of having its traditional key shape pattern, it’s a wallet-sized card that’s approximately the same size as a credit card.
-
Card Readers
If the access card is the key, the card reader is the lock that electronically reads the access card. Card readers may require cards to be inserted or held at a certain level of proximity in order to be identified. With it, your system can verify whether the access card being read is authorized or not.
-
Access Control Keypads
Normally, access control keypads are utilized in addition to or in place of the card reader mentioned above. You’ll be able to recognize this device at first glance because of its numeric keys that resemble the keys you find on touch-tone telephones. With this technology in place, people are required to enter a predetermined numeric code in order to gain access to the area.
-
Electric Lock Hardware
Most often than not, this hardware is used to control access in the entrance of a building or secured area. With it, organizations can electronically lock and unlock doors that are secured by access control systems. There are different types of electric lock hardware in the market. It can take the form of electric locks, electromagnetic locks, electric strikes, electric exit devices, etc.
-
Access Control Field Panels
Along with the other access control devices, access control field panels or intelligent controllers are installed in the buildings that are secured by access control systems. With this device, organizations gain the ability to process access control activities that are taking place in their building. Usually, you’ll be able to find these field panels in electrical, telephone, or communications closets.
-
Access Control Server Computer
Basically, the access control server computer is a device that runs a special access control system application. With this device, companies gain the ability to record their system activity as it transports information to and from access control field panels. In other words, this computer serves as the file manager and central database of the installed access control systems. With that said, you can consider this technology as the brain of your access control system.
Features You Need to Know When You’re Using Access Control Systems

As you can see, access control systems enable business owners to foster a safe working environment for their employees. With this technology, organizations gain the capacity to identify whether access cards are valid or invalid. Hence, it is a perfect way to monitor the people who come and go to your business site.
To help you understand how it does that, here is a list of the crucial access control system features that you need to know:
-
Door Status Monitoring Feature
In order for your access control system to work effectively, it’s fundamental that card reader-controlled doors are used the way they are intended. Because of this challenge, the manufacturers of this system provided a door status monitoring feature to its users. Not only does this feature help you monitor your door’s status, but also enables you to prevent its misuse.
To help you understand this feature better, here are two of its important functions:
Door-Forced-Open (DFO) Monitoring
With this function, you will be able to keep track of the incidents when your doors are opened from the outside without a valid access card and address them accordingly.
Door-Open-Too-Long (OTL) Monitoring
Aside from the DFO condition, the door status monitoring can also alert you of an OTL condition occurring. Normally, this condition sets off when the card reader door is propped open. When these conditions are triggered, its transaction records are sent to the access control server computer. Hence, enabling you to keep an eye on your card reader door’s status.
-
Automatic Unlock Feature
Other than ensuring your company’s security, access control systems also have an automatic unlock feature that can come in handy during emergency cases. For instance, when disasters like earthquakes take place, you can use this feature to allow card reader doors to be opened without an access card. With that said, this feature can help you ensure the safety of your employees.
-
Reporting Feature
One of the helpful features access control systems have is the reporting feature. When you have this in place, you gain the capacity to collect a record of system transactions in your building. The collection of these reports are often referred to by experts as a system journal.
As mentioned earlier, access control systems have the capacity to record OTL and DFO conditions—but that’s not all it can monitor. Apart from the two mentioned, this feature can also enable you to record the following system transactions below:
Valid Access – A door entry where users utilized a valid access card.
Invalid Access Attempt – This system transaction refers to the instances when you use an access card at the wrong place or at the wrong time.
Equipment Failure Condition – This system transaction condition occurs whenever it detects a wiring-related failure on the access control system of your building.
Power Failure Condition – This access control system condition is triggered by the loss of primary power.
Things to Set Up Before You Enable Access Control Systems
Before your access control system can go up and running, there are certain settings and requirements that you should configure in your system. You can accomplish this task easily at the host computer of your access control software. By doing this, you’ll be able to boost your system’s security performance.
To guide you in this matter, here is a list of things you should set up prior to the implementation of your system:
-
Doors
When you install an access control system in your building, you have the power to set whether the access card can access all card reader-controlled doors or not. With that, you’ll be able to control the people who can access certain areas in your building and boost your company’s safety and security.
-
Time of Day
Aside from configuring doors, you should also configure the time when the system will allow the cardholders to access certain areas. You can allow it to work 24 hours a day or during operation hours.
-
Day of Week
One way to fend off internal security issues is by setting the days of the week when access cardholders are granted access in your building. Instead of allowing everyone to enter your business premises every day, you can set it to function only on their workdays. Furthermore, you can also set your access control system to work differently on holidays. Through this, you’ll be able to boost your company’s security and deter security breaches from occurring.
-
Start and Stop Dates
If your business has contractual workers, then you’ll appreciate the access control system’s ability to set a start and stop date for access. In your access control software, you can define the date range when an access card will work in your building. By doing this, you’ll be able to make sure that your contractual workers will no longer have access to your business premises when their contract is over.
Many IT professionals today consider access control systems as a reliable solution to strengthen an organization’s security. If you want to install this security system in your business site the right way, then it’s best that you contact reputable IT service providers like House of I.T. With their expertise, you’ll be able to have an access control system that is perfect for your business needs. Aside from that, they can also assist you to make the most of the system’s capabilities for a long time.
Acquire the best access control system for your company by contacting the help of House of I.T now.
Recent Posts
- How Does GPON Improve Network Efficiency?
- What Are The Advantages Of GPON?
- What’s The Deal With Ransomware Attacks?
- Are GPON Providers Widely Available?
- What’s GPON’s Impact On Bandwidth?
- Why Is Multi-Factor Authentication Important?
- What’s The Significance Of ONT In GPON?
- Are GPON Networks Easy To Maintain?
 Blogs
Blogs Infographics
Infographics Videos
Videos Podcasts
Podcasts Case Studies
Case Studies Call For Quote
Call For Quote